Peerless Tips About How To Detect A Ddos
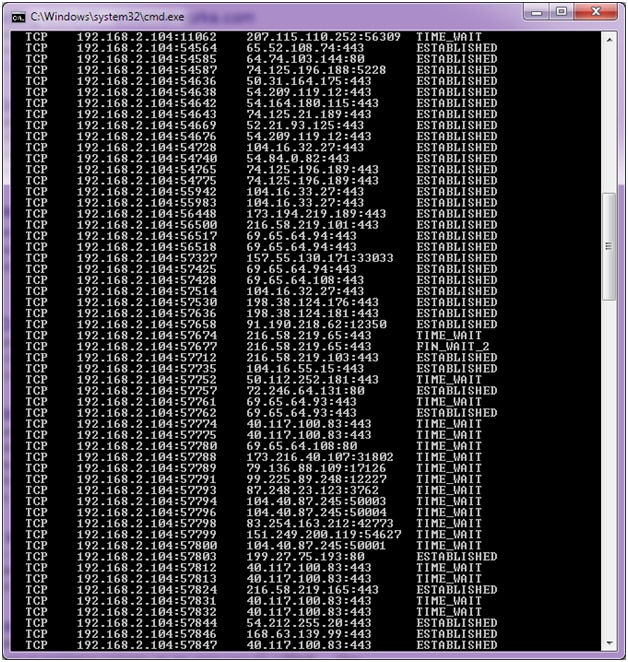
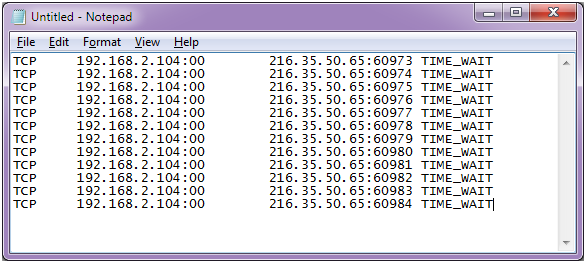
Certain ip addresses send too many connection requests over a short time.
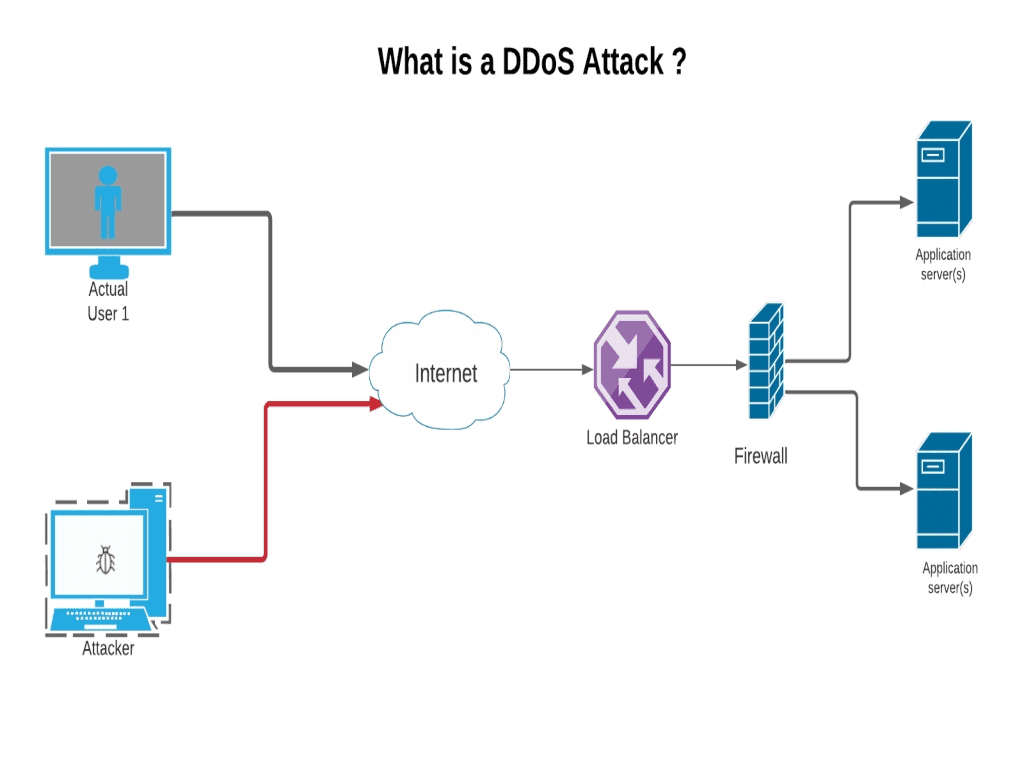
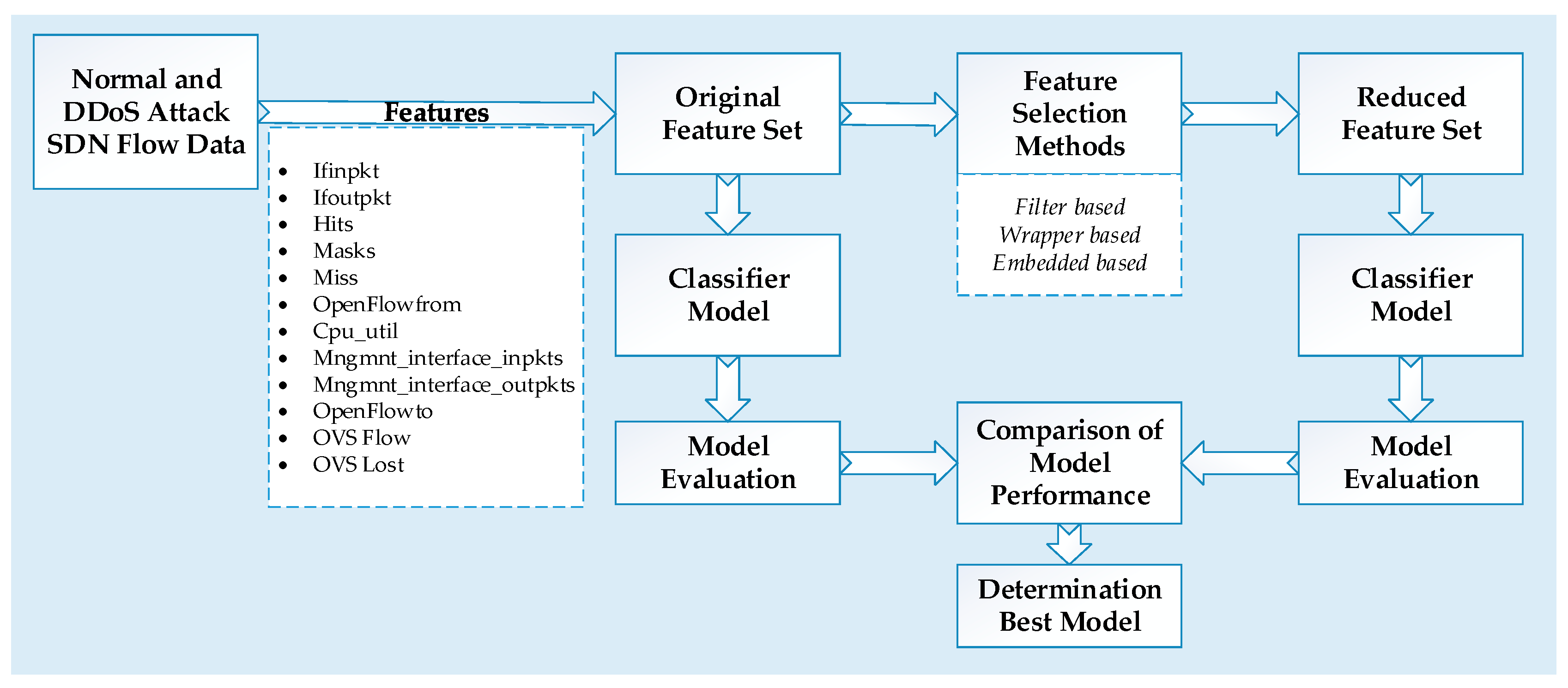
How to detect a ddos. This will generate standard output. To detect attacks, both types need to be independently monitored; However, a recent disproportionate spike in.
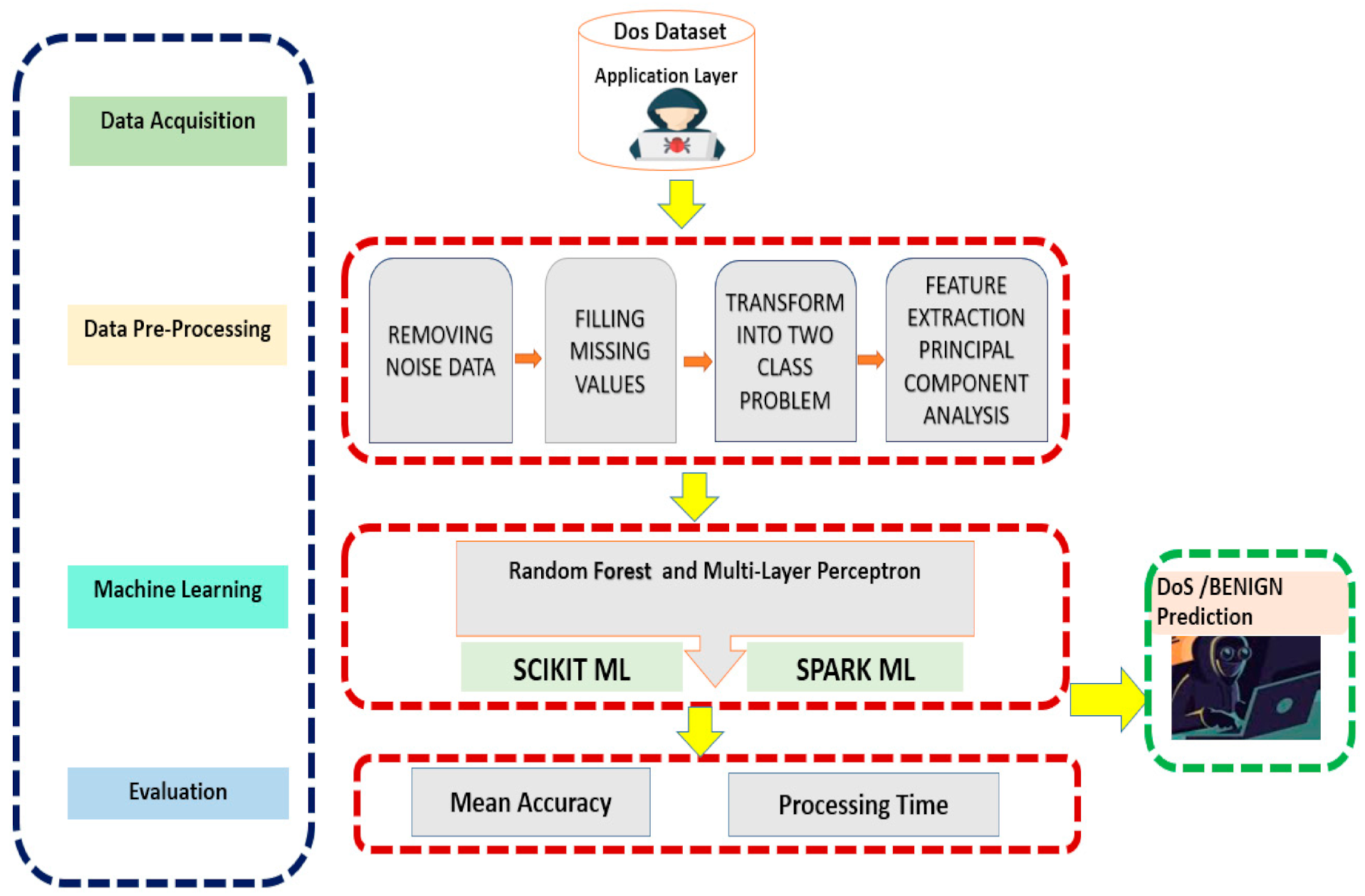
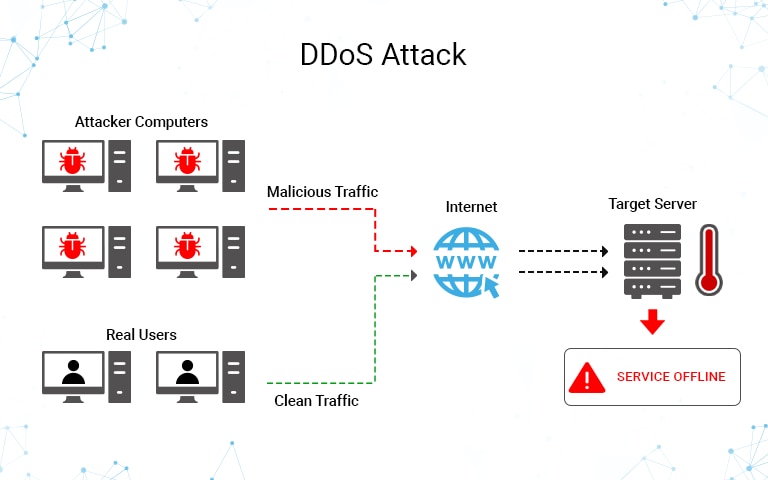
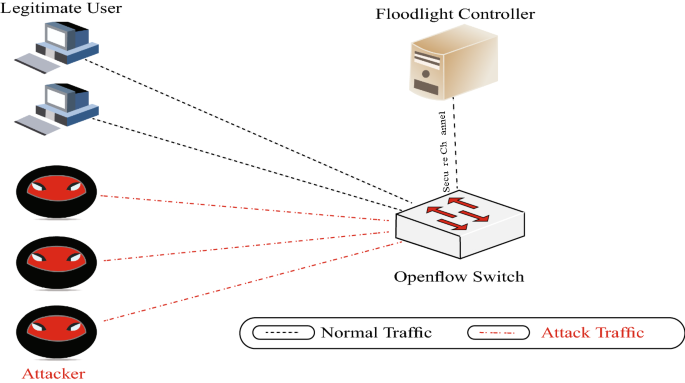
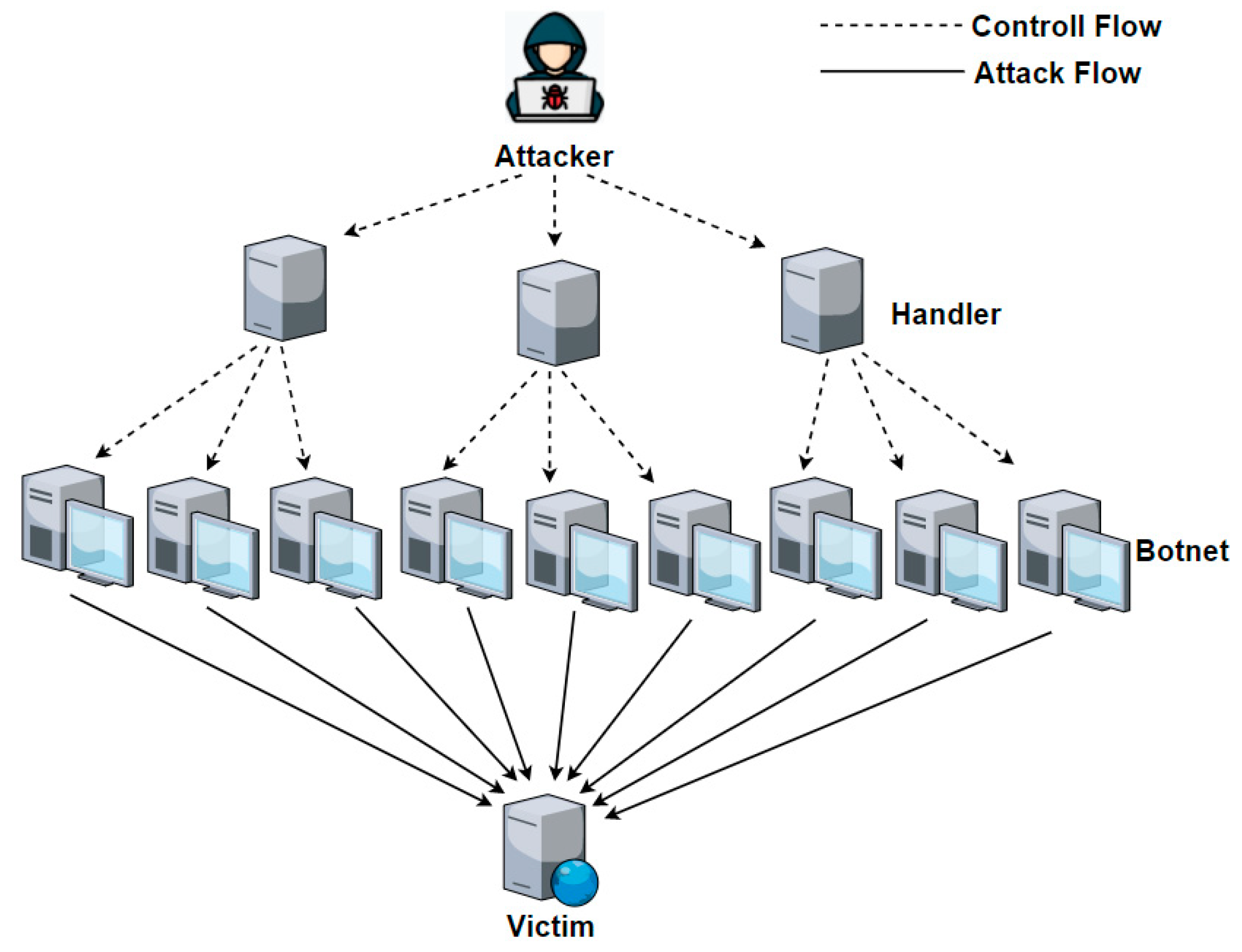
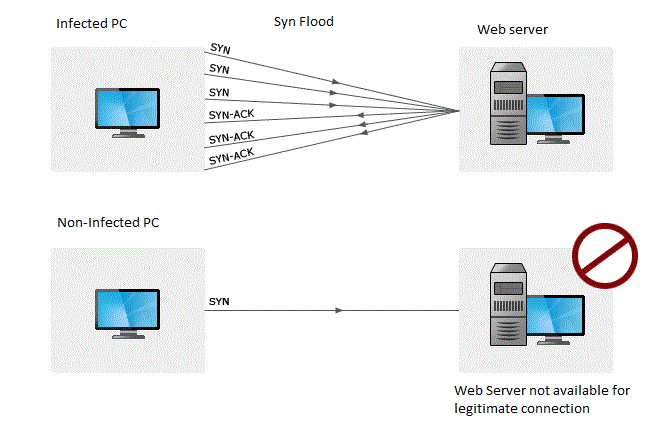
Distributed denial of service (ddos) attacks is a subclass of denial of service (dos) attacks. A denial of service (dos) attack is a malicious attempt to affect the availability of a targeted system, such as a website or application, to legitimate end users. Logs contain raw data with loads of information.
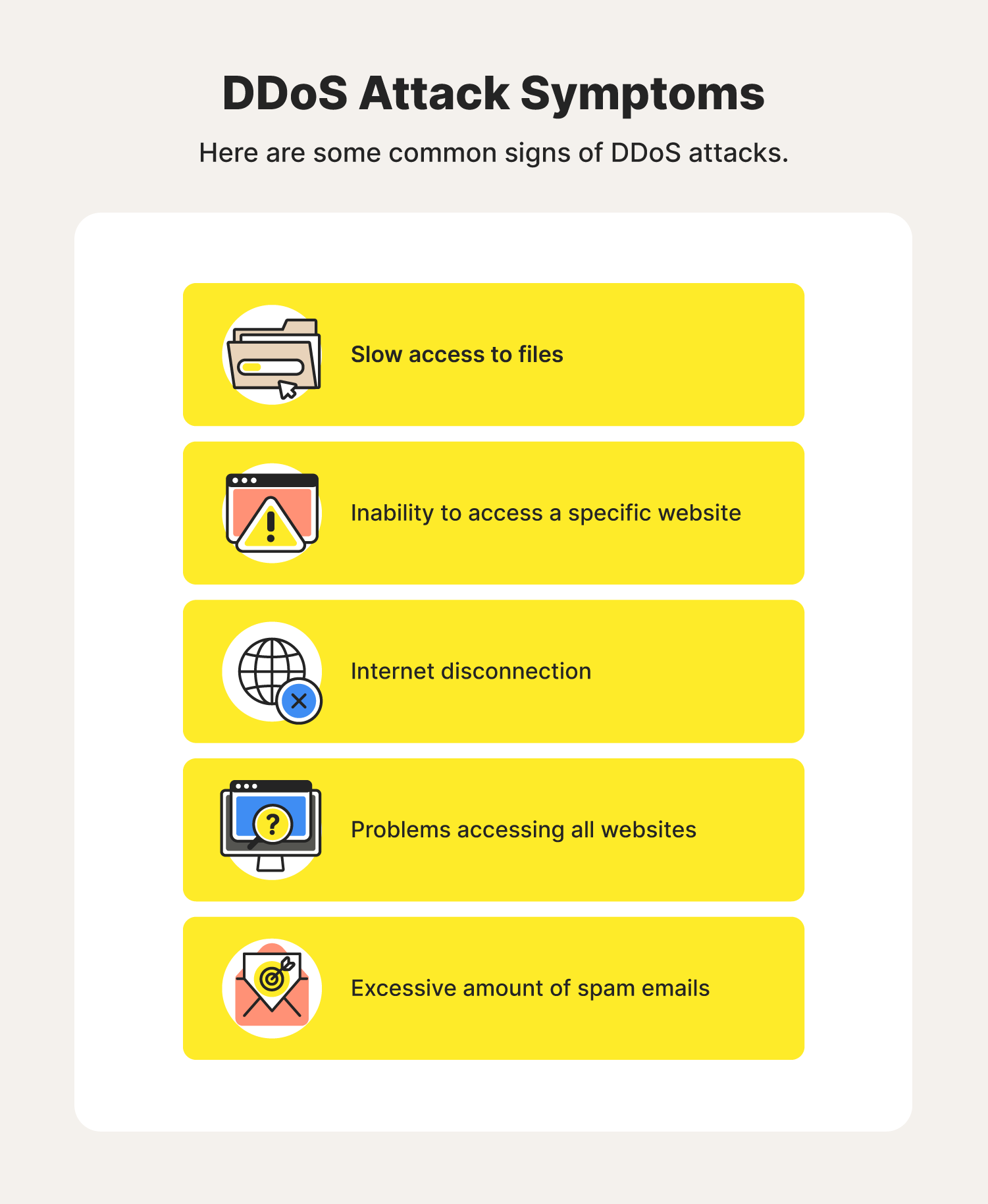
How to check for ddos. You can also check your network stats and. You see a surge in web traffic, seemingly out of nowhere, that’s coming from the.
You can set lfd to detect suspicious directories: Dns uses two types of packets: If yes then your server is fine and if see.
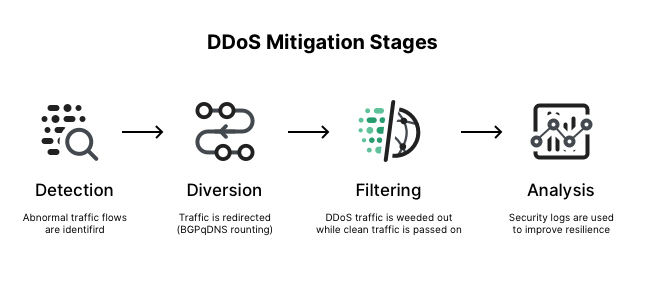
Within an hour of compromise, azure security center used microsoft’s threat intelligence to detect that the compromised subscription was likely being used as a shadow. Once you know how a ddos attack works, you can use. A graphical representation of the same is an easier way to understand abnormalities and guess a potential ddos attack.
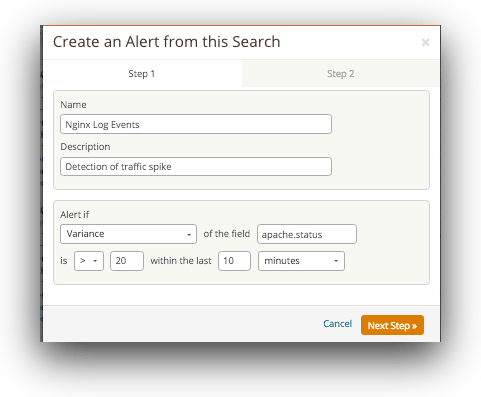
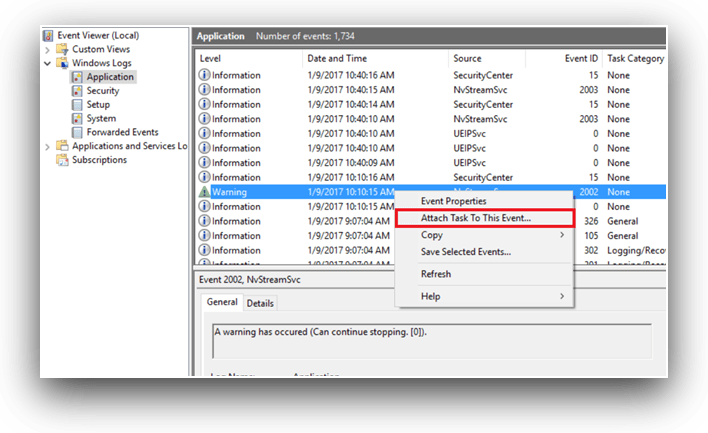
If you’re concerned that your server might be under ddos attack, the first thing you’ll need to do is take a look at the load on your server. 5 red flags when detecting ddos attacks. Log monitoring is the best and the most effective way for quick identification of a ddos threat.
Typically, these connections don’t get completed since. Dns request and dns response. While there’s no one way to detect a ddos attack, there are a few signs your network is under assault:
Something as simple as the. Lf_dirwatch = “300.” when you enter the following command, your server will display a list of ips connected to your server. A ddos attack involves multiple connected online devices, coll.




.png?width=1940&name=op%20(1).png)